With the rise of cybercrime as a service business model, the information necessary to organize an attack is in demand among cybercriminals. Kaspersky’s experts analyzed nearly 200 posts on the dark web offering to buy information for initial access to companies’ systems. The average cost for access to a big company’s systems lies between $2000 and $4000, which is relatively inexpensive compared to the potential damage it could cause targeted businesses. Such services are of prime interest to ransomware operators, whose profits could reach up to a whopping $40 million a year. These and other findings can be found in the new Kaspersky report, ‘How much does access to corporate infrastructure cost?’.
Kaspersky research revealed a high demand on the dark web not only for data obtained through an attack but also for the data and services necessary to organize one (e.g., the data needed to perform specific steps of a multiphase attack). Once an attacker gains access to the organization’s infrastructure, they can sell that access to other advanced cybercriminals, such as ransomware operators. Such attacks result in significant financial and reputational losses to the targeted organization and may even cause a suspension of work and disruption to business processes. SMBs and enterprises are both targeted by these attacks.
Company experts analyzed nearly 200 posts on the Dark web offering to buy the information for initial access to companies’ forums, intending to define the main types of corporate data sold, as well as which criteria cybercriminals use to evaluate the price for an organization’s data. Most o posts (75%) were selling RDP (Remote Desktop) access. It provides access to a desktop or application hosted remotely, then allows cybercriminals to connect, access, and control data and resources via a remote host as if a company’s employees were controlling the data locally.
The prices for the initial access vary greatly from a couple of hundred dollars to hundreds of thousands. Unsurprisingly, the key determinant for the high prices of the analyzed offers is the potential victim’s revenue – the price grows alongside the revenue. The prices might also differ depending on the company’s industry and operating region.
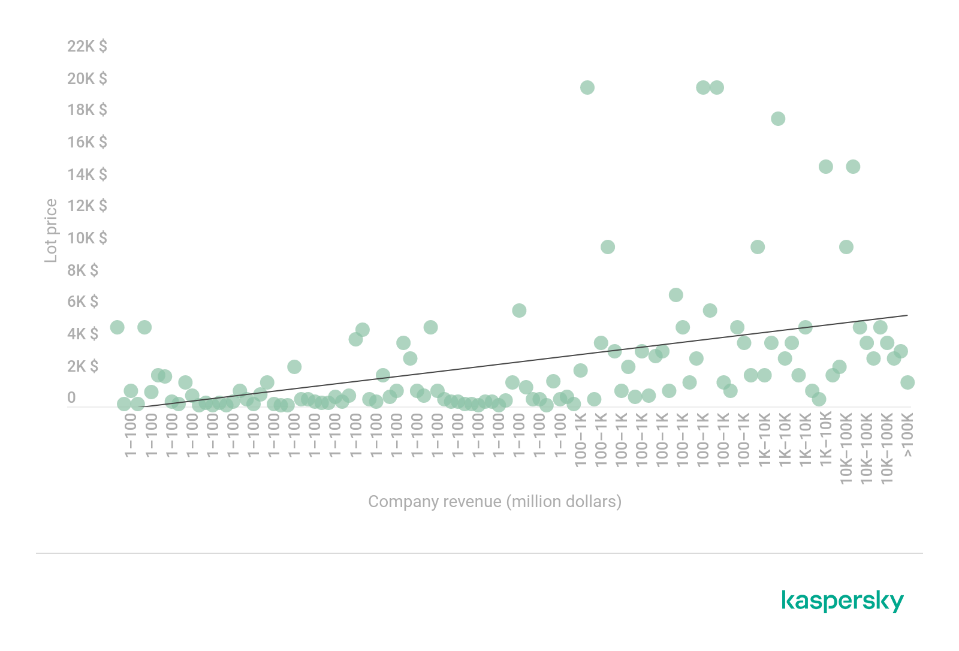 The correlation between the price of network access data and a company’s revenue
The correlation between the price of network access data and a company’s revenue
Access to large business infrastructures usually costs between $2,000 and $4,000, which are relatively modest prices. But there is no upper limit to the cost either. Data belonging to a company with a revenue of $465 million is for sale for $50,000.
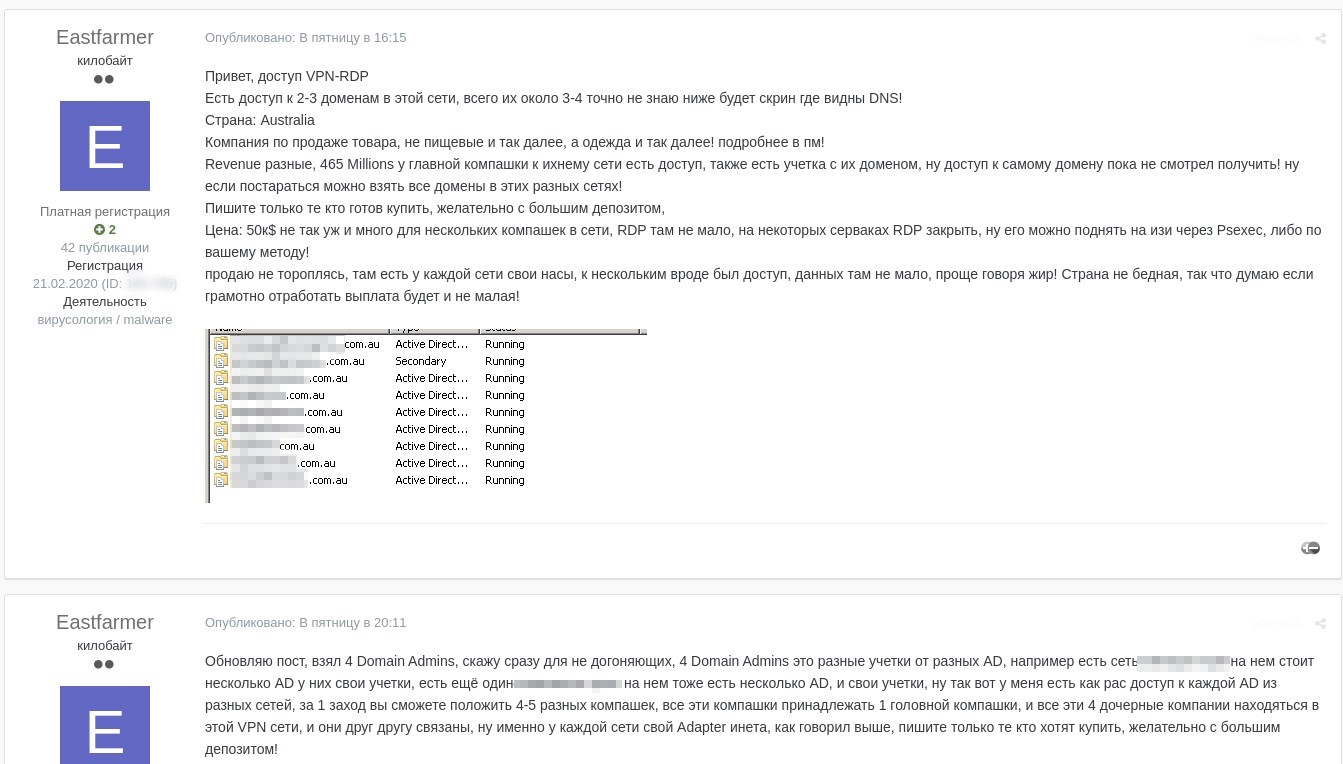 An example of a sale offer on data for remote access to five companies in one network for $50,000
An example of a sale offer on data for remote access to five companies in one network for $50,000
Undoubtedly, one of the most important components of the initial access price is the amount of money the buyer can potentially earn from an attack using that access. Ransomware operators are ready to pay thousands, or even tens of thousands, for the opportunity to infiltrate a corporate network for a reason. These often cost the targeted corporation millions of dollars. The most prolific actors from the past year have potentially received $5.2 billion in transfers over the last three years.
As well as encrypting corporate data, cybercriminals also steal it. They may later post some of the stolen data in their blogs – primarily as proof, but also for extra leverage – threatening to publish more unless the company pays them the money they demand within a stipulated timeframe.
‘The cybercriminal community has evolved, not only from a technical point of view, but from the standpoint of their organization. Today ransomware groups look more like real industries with services and products for sale. We constantly monitor darknet forums to detect new trends and tactics of the cybercriminal underground. We’ve observed the increasing market of data required to organize an attack. Gaining the visibility of sources across the dark web is essential for companies seeking to enrich their threat intelligence. Timely information about planned attacks, discussions around vulnerabilities, and successful data breaches will help to reduce the attack surface and lead appropriate actions.’ comments Sergey Shcherbel, security expert at Kaspersky.
























