A detailed look at a phishing site masquerading as an e-mail scanner and its attempts to snag victims.
In recent years, news about e-mail-based infections of corporate networks has been fairly regular (and generally connected with ransomware). So, it’s no surprise that scammers periodically use the topic to try to extract credentials for corporate mail accounts by persuading company employees to run a scan of their mailbox.
The ploy is aimed at people who know about the potential threat of malware in e-mail but have insufficient understanding of how to deal with it. Infosec personnel would do well to explain the tricks to employees and use such examples to illustrate what employees should look for to avoid falling victim to cybercriminals.
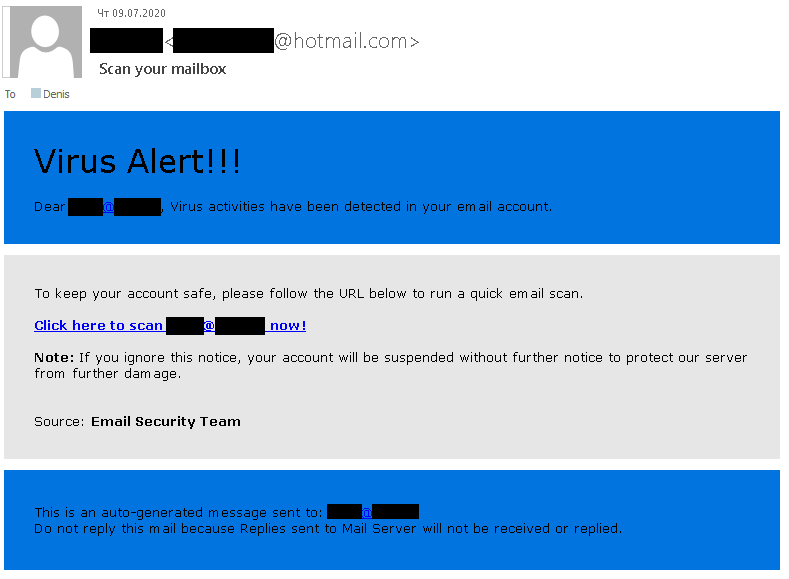
Phishing e-mail
This scam message employs the time-honored trick of victim intimidation. You can see it right in the header, which reads “Virus Alert” followed by three exclamation points. However trifling punctuation may seem, it’s the first thing that should tip off the recipient that something may be wrong. Unnecessary punctuation in a work e-mail is a sign of drama or unprofessionalism. Either way, it’s inappropriate in a notification supposedly intended to convey information about a threat.
The number one question the recipient should ask is: Who sent the message? The e-mail states that failure to act will result in the recipient’s account being blocked. It might be logical to assume that it was sent either by the IT service that supports the corporate mail server or by employees of the mail service provider.
But it’s important to understand that no provider or internal service would require user action to scan the contents of the mailbox. Scanning takes place automatically on the mail server. Besides, “virus activity” rarely occurs inside an account. Even if someone did send a virus, the recipient would have to download and run it. Infection happens on the computer, not in the mail account.
Coming back to that first question, a look at the sender raises two immediate red flags. First, the e-mail was sent from a Hotmail account, whereas a legitimate notification would display the domain of the company or provider. Second, the message is said to come from the “Email Security Team.” If the recipient’s company uses a third-party mail service provider, its name is bound to appear in the signature. And if the mail server is in the corporate infrastructure, the notification will come from in-house IT or the infosec service — and the chances of an entire team being responsible solely for e-mail security are minimal.
Next is the link. Most modern e-mail clients show the URL hidden behind the hyperlink. If the recipient is urged to click through to an e-mail scanner hosted on a domain that belongs to neither your company nor the mail provider, it is almost certainly phishing.
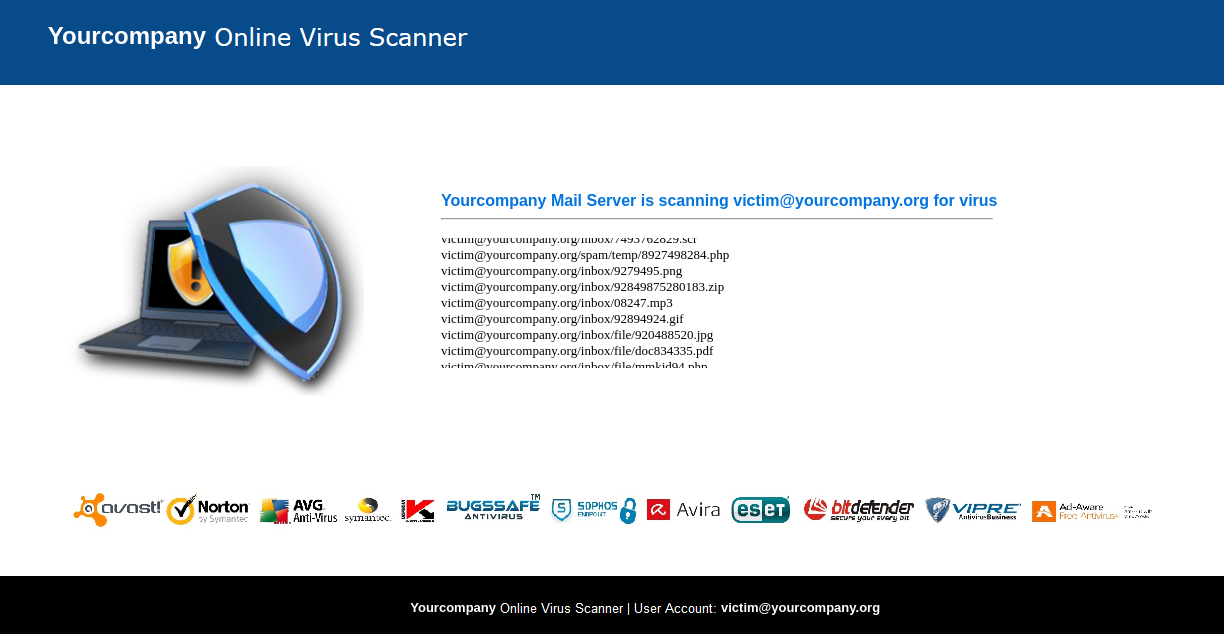
Phishing site
The site looks like some kind of online e-mail scanner. For the appearance of authenticity, it displays the logos of a host of antivirus vendors. The header even boasts the name of the recipient’s company, which is meant to remove any doubt about whose tool it is. The site first simulates a scan, then interrupts it with the ungrammatical message “Confirm your account below to complete Email scan & delete infected all files.” The account password is required for that, of course.
To ascertain the nature of the site, start by examining the contents of the browser address bar. First, as mentioned above, it’s not on the right domain. Second, the URL most likely contains the recipient’s e-mail address. That in itself is fine — the user ID could have been passed through the URL. But in case of any doubt about the site’s legitimacy, replace the address with arbitrary characters (but keep the @ symbol to maintain the appearance of an e-mail address).
Sites of this type use the address passed by the link in the phishing e-mail to fill in the blanks in the page template. For the sake of the experiment, we used the nonexistent address victim@yourcompany.org, and the site duly substituted “your company” into the name of the scanner, and the entire address into the name of the account, whereupon it appeared to start scanning nonexistent attachments in nonexistent e-mails. Repeating the experiment with a different address, we saw that the names of the attachments in each “scan” were the same.
Another inconsistency is that the scanner supposedly scans the contents of the mailbox without authentication. Then why does it need the password?
How to protect your employees from phishing
We have analyzed in detail the signs of phishing in both the e-mail and the fake scanner website. Simply showing this post to employees will give them a rough idea of what to look for. But that is just the tip of the proverbial iceberg. Some fake e-mails are more sophisticated and harder to sniff out.
Therefore, we recommend continuous awareness training for employees about the latest cyber threats — for example, using our Kaspersky Automated Security Awareness Platform.